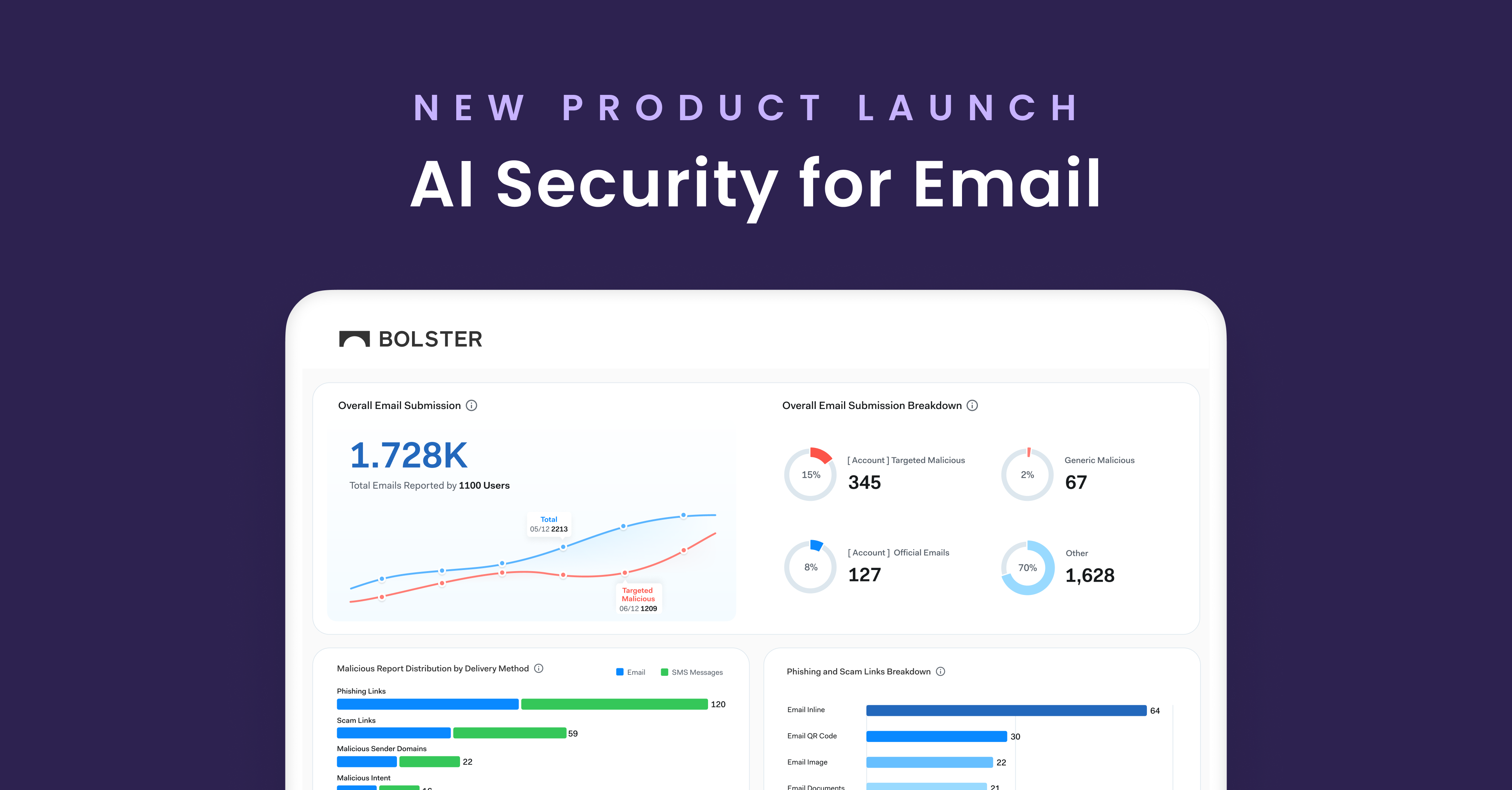
Bolster is excited to share a major landmark in our path to making the internet a safer place…

The Bolster Blog
Thought provoking blogs discussing recent trends on digital risk protection services, phishing protection, threat intelligence, artificial intelligence, machine learning, brand protection and more!
Recent Posts
The Click That Stole Holidays: Black Friday and Cyber Monday Scams Unmasked
Introduction The onset of Cyber Monday and Black Friday deals is something we all stay up for. Whether it’s discounted vacation travel packages, instructional offers.
Exploring the Risks of IPFS in Phishing Attacks
Introduction The InterPlanetary File System (IPFS) is a cutting-edge technology designed to revolutionize how we store and share data across the internet. It offers a.
Phishing in Focus: Bolster's 2024 Mid-Year Phishing and Online Scam Update
With the unprecedented surge in phishing attacks sparked by AI, protect your business with data into key phishing and scam trends including election fraud, industry-targeting, and consumer interest scams.
Beyond the Perimeter: Securing Your Brand with Customer-Focused Phishing Defense
In today’s digital landscape, email continues to be a primary…
Credit Union Scams: How Cybercriminals Are Targeting Small Credit Unions in the US
In recent months, Bolster’s research team has identified a surge…
Understanding Domain Reputation Attacks and How to Protect Your Brand
Without even defining the term, you could probably guess that…
Is This a Phishing Link? How to Limit Risk Before Clicking.
Can you imagine a world without hyperlinks? They have become…
Understanding Prepending and Its Role in Cybersecurity Threats
Another day, another cybersecurity threat you should be aware of…
Social Engineering: The Gateway to Phishing Attacks
Cybersecurity threats continue to be an ever-present danger, and among…
In-Session Phishing is Becoming An Advanced Cybersecurity Threat
Phishing remains pretty much synonymous with “cyber attacks” as bad…
Cracking the Shield: Methods Hackers Use to Bypass MFA
Multi-Factor Authentication (MFA) has emerged as a fundamental element in…
Understanding Man-in-the-Middle Phishing: A Deep Dive into Evilginx
Phishing continues to be one of the most popular ways…
Understanding Telegram Carding: The Dark Side of Digital Transaction
In the huge evolving rolodex of cybersecurity threats, carding remains…
How to Find and Remove Spyware From Your Phone
Learning how to find and remove spyware from your phone…
Browser-in-the-Browser (BitB) Phishing Attacks & Their Potential Impact on Businesses
Attackers continuously create new techniques in the ever-changing field of…